The only cybersecurity course online that offer real-time attack simulations are the ones built around live labs, h2kinfosys, SOC-style training, etc. If you’re looking for cyber security training online, you want something that actually allows you to experience an attack, not just learn about it.
So, what does “real-time attack simulation” actually mean?
This section of the text was a little confusing to me at first. A lot of the online cybersecurity course claim to offer live labs, etc., but the truth is that they’re usually just step-by-step tutorials where you know exactly what the outcome is going to be.
Real-time attack simulation is a little different.
You’re placed into an environment where:
Alerts are going off (like you’re actually in a SOC)
- Logs are messy and incomplete
- You have no idea if it’s a false positive or an actual breach
- And yes… sometimes you’re going to make the wrong call
That’s the point of the training. It’s a little messy, a little stressful, and honestly the only cyber security training online I’ve come across that actually simulates real cyber security jobs.
The types of courses that actually get this right
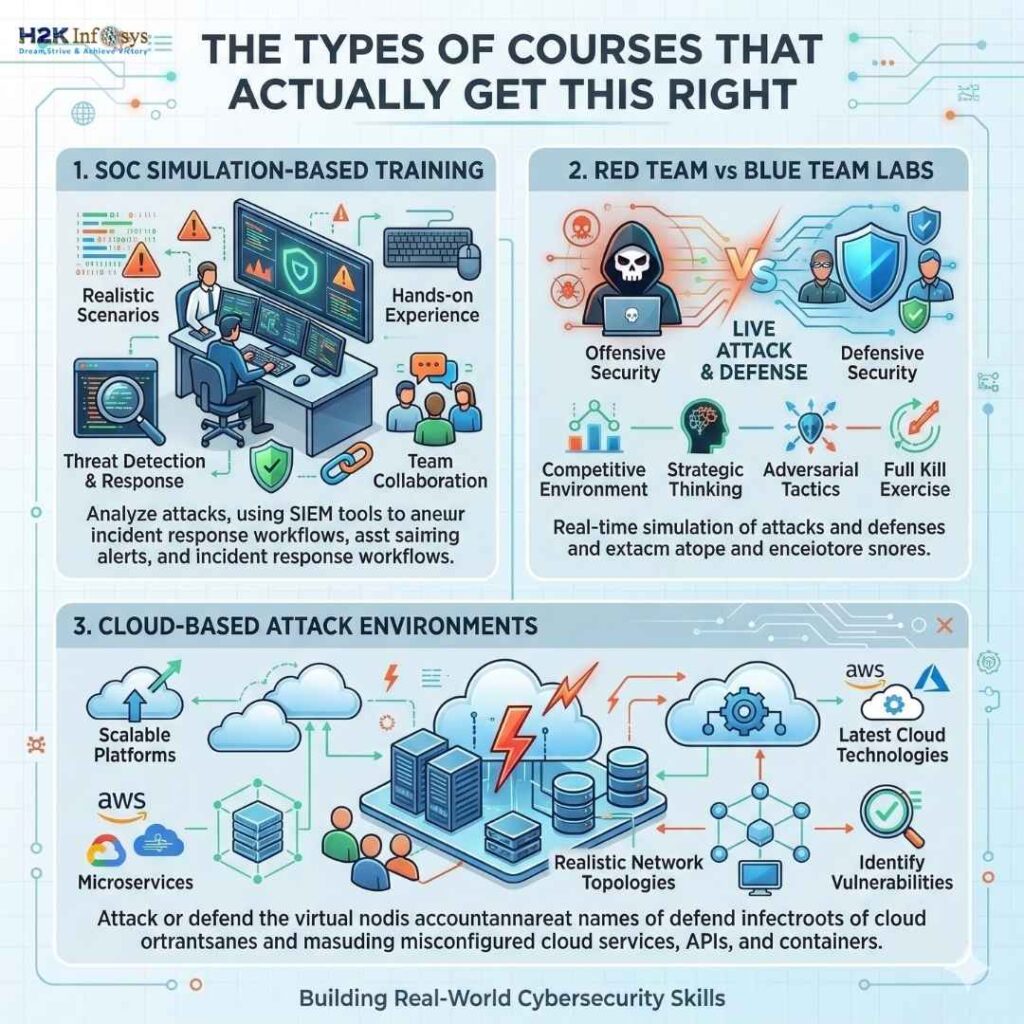
From what I’ve come across (as well as talking to various individuals who have been through various training programs), the only training styles I’ve come across that actually offer real-time attack simulations are the following:
1.SOC Simulation-Based Training
These are probably the closest to real-world cybersecurity course jobs you’re going to find.
You’re essentially working within a simulated Security Operations Center environment where you’re:
Monitoring SIEM tools
Investigating alerts
Escalating alerts
Writing reports
It feels like you’re actually doing the job you’re training for, not like you’re “learning” the job.
2.Red Team vs Blue Team Labs
This is where things get interesting.
Red Team → play the attackers
Blue Team → defend and detect
There are some advanced tools out there which allow you to do both, and it totally flips your thinking around. Once you get a sense of how attackers move around, defending becomes much easier.
3.Cloud-Based Attack Environments
Most companies are moving to cloud environments – AWS, Azure – so modern attacks are happening there too.
The good training programs out there now include:
Misconfigured S3 bucket scenarios
IAM privilege escalation scenarios
API exploitation scenarios
It’s super relevant training right now, especially with the cloud breach explosion we’ve seen over the last two years.
Where most training programs fall short (and why you get lost)
Here’s the honest truth…
Most “cyber security training online” programs out there still use:
Pre-recorded videos
Static environments for training
Lack of real-time feedback and interaction
You complete them all and get a certificate, then struggle through an interview process because you never get any real-world experience.
This is exactly why many students don’t translate well into a cybersecurity course job after training, even after months of training.
What to look for in a real simulation-based training program
If you’re considering training options out there, here’s what you should really look for:
Live instructor training sessions (not videos!)
Live environments for training which update and change constantly
Incident response flows (ticketing, escalation, reporting)
Exposure to tools like Splunk, QRadar, or Microsoft Sentinel
Mentor feedback when you get lost (this last one is huge!)
One thing I think is underrated training programs which incorporate a little bit of cybersecurity course sales training. Sounds silly, but having the ability to articulate a problem for a customer is huge!
A quick real-world cybersecurity course example
My friend recently had to go through a simulation-based cybersecurity course training program where they had to investigate a ransomware attack scenario.
They weren’t told what it was.
They were just told:
Unusual login patterns detected
File encryption alerts detected
Suspicious outbound traffic detected
They had to piece it all together and confirm the attack and recommend containment.
This was more than they could have learned in weeks of theory.
Where H2K Infosys comes into play
Just as we were exploring all these training programs, h2kinfosys was mentioned a lot, especially because their training methods are based around live project environments and simulations.
From what I have seen so far, their training methods try to bridge the gap between training and actual job environments, which is what students are mostly lacking.
One last thought (the real version)
If a training cybersecurity course does not make you slightly uncomfortable at some point and requires you to think and figure out what you’re doing, then it probably does not teach you much for the real world.
The best training for cybersecurity jobs with training does not feel smooth.
It feels real.
And that is what makes all the difference when you finally get out into the real world.