Typically, it takes between 6 to 12 months of regular online training, and with some programs, such as H2K Infosys, a heavy focus on practical exercises, to become proficient enough to begin applying for entry-level positions in cybersecurity. The timeframe is heavily dependent on your background in IT, how thorough your training program is, and whether it includes hands-on labs or real-world cyber security training and job placement assistance.
Let’s attempt to analyze what this journey entails in pragmatic terms.
What Proficiency in Cybersecurity Means
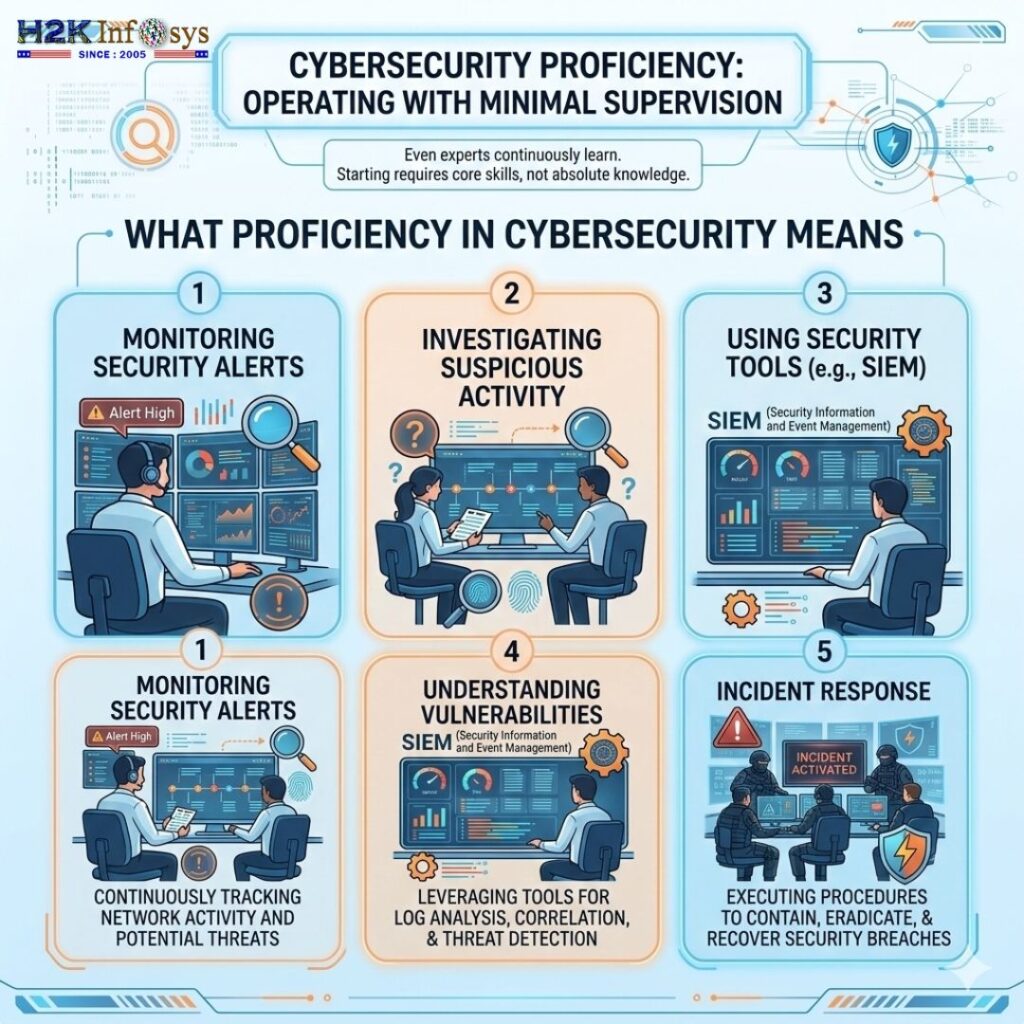
To begin with, it is important to provide some context to what proficiency means in cybersecurity.
To begin working in this domain, it is not necessary to have a wealth of knowledge concerning cybersecurity. Even those with extensive experience in this area have to learn continuously due to the almost daily changes in the threat landscape. Proficiency entails being able to complete the following tasks with minimal supervision:
– Monitoring security alerts
– Investigating suspicious activity
– Understanding vulnerabilities of a given network
– Using security tools such as SIEM
– Incidence responses
At that level, your training should have sufficiently prepared you to start applying for cybersecurity positions that are geared towards entry-level positions such as Security Analyst, SOC Analyst, or Cybersecurity Technician.
Pathways for Cybersecurity Training
Individual experiences differ, but most learners complete structured online training using a fairly consistent sequence.
Months 1 and 2: Learning the Fundamentals
The first phase focuses on foundational knowledge regarding cybersecurity and the IT systems.
You typically cover:
• Basic networking (TCP/IP, DNS, ports)
• Operating systems (Linux and Windows)
• Fundamentals of cybersecurity
• Various types of threats and overall attack vectors
• Basic security concepts, such as encryption and authentication
This phase may appear overwhelming, especially for a learner who lacks a technical background. However, once the concepts of networking begin to click, everything else tends to follow suit.
Students quickly assess that the elements of cybersecurity are not what are typically sensationalized in the media. There are no movies about hacking and tools that jazz up the profession. Instead, it is the knowledge and understanding of underlying systems in detail.
Months 3 and 4: Security Tools and Practical Skills
Once the foundational knowledge is established, training focuses on hands-on tools and strategies for defense.
You may begin engaging with:
• Security Information and Event Management (SIEM) tools for monitoring logs
• Vulnerability scanners
• Packet analyzers such as Wireshark
• Threat intelligence frameworks
• Incident response workflows
This is where training programs separate themselves through excellence. Those that provide cybersecurity training with job placement typically incorporate elements such as cyber attack simulations, laboratory environments, and exercises that enliven SOC (Security Operations Center) monitoring.
I would say the laboratories are the first places where I start to build real confidence. Seeing a simulation of an attack happen and recognizing it in the logs is quite the pleasure.
Months 5-6: Certifications and Practice in the Real World
At this point, a lot of learners are registering for certifications like:
– CompTIA Security +
– CEH (Certified Ethical Hacker)
– Cybersecurity Analyst certs
Certifications are not everything, however, they do give employers a way to check your skills.
More importantly, this phase tends to include:
– Building a security portfolio
– Finishing a real-world laboratory work
– Practicing scenarios for incident responses
– Learning how to document and report
Cyber security training and job placement programs usually begin preparing for a career in this phase.
Months 7-12: Job Ready and Specialization
After the core skills are available, learners typically begin to concentrate on career readiness.
This includes:
– Cybersecurity role resume writing
– Mock technical interviews
– Security case study analyses
– Threat detection hands on exercises
Some learners begin to look for specific areas of cybersecurity like:
– Cloud security
– Threat hunting
– Security automation
At this point, a lot of learners start to apply for cybersecurity role jobs with the aid of training support programs.
Real-World Example: A Typical Career Switch
In the case of an individual moving from IT support to cyber security, the example is commonplace.
Below is a sample outline of a training program commencing during a single month of a calendar year.
Month 1–2: Introduction to Networking and Linux
Month 3–4: Introduction to tools for security focused monitoring.
Month 5–6: Obtain Security + Certification.
Month 7–9: Apply for roles relative to Security Operations Center Analysts.
In general, individuals can expect to receive their first roles focused on the monitoring of security alerts and assisting in vulnerability management within a timeframe of 8 to 10 months after starting the program.
As is evidenced by the rest of the world’s cyber security field, trained entry level candidates remain very much in demand.
What Influences the Speed of Learning Cybersecurity?
Professionally developed learning targets for all individuals enrolled in a program. Learning in the field of Cyber Security is no different, there is a finite number of learning targets in place and given the multiple combinations of components the actual time taken to achieve proficiency is highly variable.
Your Tech Background
Your understanding of Networking, Linux or programming is the base from which you will progress.
Perhaps someone with a background in IT Support will reach a point of employability in 6 months while someone starting with no background may not reach the same level for 9 to 12 months.
The Effectiveness of Your Training Program
The majority of your program’s training being video lectures will, on average, result in you learning more slowly than the majority of your peers.
It is reasonable to expect that the majority of peers will achieve proficiency sooner than you if the following is true:
– your program includes multiple video lectures
– you are trained in a modern cyber security discipline (of)
– your program includes multiple cyber security drills focused on training for the profession (and)
– your program provided you with a position in the field
– your program provides you access to a simulation of a cyber security environment in which you may practice in an unencumbered environment.
Daily Practice Time
Cybersecurity is very skill-based.
People who practice 2–3 hours daily with labs and exercises usually progress much faster than those that study only on the weekends.
Why Cybersecurity Training Is So Popular Right Now
Cybersecurity has become one of the fastest growing technology careers in the world.
Due to the high profile attacks such as ransomware in restraining the hospitals, supply chains and even government systems, many organizations have started to put more focus on building out their security teams.
Typically, organizations such as the Cybersecurity and Infrastructure Security Agency have been warning us of the increase of cyber threats directed to organizations of all sizes.
Due to this, organizations are looking more towards candidates who have gone through a rigorous cyber security training followed by a structured internship with a job guarantee as they want to employ people who have the skill of threat recognition and not just theoretical knowledge.
Signs You’re Becoming Proficient in Cybersecurity
- You should be able to tell the training is paying off when the following begins to happen:
- Security logs start making sense to you and no longer appear as random data
- You start recognizing the patterns of anomalous network traffic
- You grasp the knowledge of the mechanisms behind the attacks
- You are able to clearly articulate the vulnerabilities to a sufficient level yourself to educate someone else
It is a gradual process and one day you find yourself analyzing the alerts instead of just looking up the definition of all the terms one by one.
That is the point where you can say you have attained a high level of proficiency.
Conclusive remarks
Gaining expertise in cybersecurity through internet-based instruction usually ranges from six to twelve months, particularly when it involves elements like live labs, credentialing, and career counseling. Job placement coupled with live labs in cybersecurity training facilitates faster learning and provides an instant transition to a cybersecurity jobs with training available in security operations center and IT security team positions.
It is not about how quickly you can accomplish something. It is about deliberate and consistent practice, along with exposure to real-world environments. Cybersecurity is one of the few fields that is rewarding to those who remain inquisitive, tinker with different tools, and continually gain knowledge in response to evolving threats.