What Is Ethical Hacking?
Introduction
Cyber threats have grown in scale, sophistication, and automation. Organizations now face ransomware attacks, data breaches, supply-chain compromises, and insider threats on a daily basis. Traditional security tools alone are no longer sufficient to protect complex digital ecosystems.
This is where ethical hacking plays a critical role. By thinking and acting like an attacker, without criminal intent, security professionals can expose real weaknesses that automated tools often miss. Ethical hacking allows organizations to move from a reactive security model to a proactive, prevention-focused approach.
Key drivers behind the growing importance of include:
- Rapid adoption of cloud computing and remote work
- Increased attack surfaces from APIs, IoT, and SaaS platforms
- Strict regulatory and compliance requirements
- High financial and reputational costs of data breaches
Ethical Hacking vs Illegal Hacking
Although the technical methods may appear similar, it is fundamentally different from illegal hacking.
| Aspect | Ethical Hacking | Illegal Hacking |
| Authorization | Explicit written permission | No permission |
| Purpose | Improve security | Exploit systems |
| Legal status | Lawful | Criminal |
| Reporting | Responsible disclosure | No disclosure |
| Outcome | Risk reduction | Financial or operational damage |
It is governed by laws, contracts, and professional codes of conduct, ensuring that testing activities remain legal and beneficial.
Core Objectives of Ethical Hacking
The primary objectives of ethical hacking are not limited to finding vulnerabilities. Instead, they focus on understanding real-world risk and improving security maturity.
Main objectives include:
- Discovering exploitable vulnerabilities
- Validating the impact of security flaws
- Testing incident detection and response
- Strengthening defensive controls
- Supporting compliance and audit requirements
Through ethicalhacking, organizations gain insight into how attackers might compromise systems and how defenses can be improved.
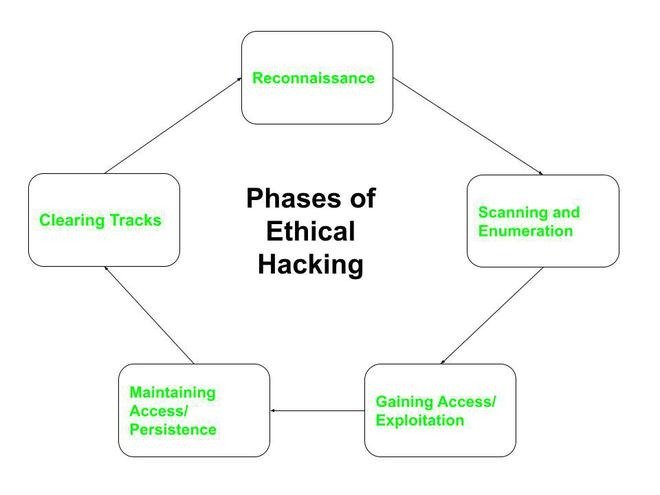
The Ethical Hacking Lifecycle
It follows a structured methodology to ensure accuracy, repeatability, and accountability.
1. Reconnaissance (Information Gathering)
This phase involves collecting publicly available and authorized internal information such as IP addresses, domain names, employee email formats, and exposed services.
2. Scanning and Enumeration
Security testers identify live systems, open ports, running services, and software versions. This phase reveals potential entry points for attackers.
3. Exploitation
During exploitation, ethicalhacking techniques are used to safely test whether identified vulnerabilities can actually be exploited. This step demonstrates real business risk rather than theoretical weaknesses.
4. Privilege Escalation and Lateral Movement
Testers evaluate whether limited access can be expanded into higher-level privileges or movement across systems.
5. Reporting and Remediation
The final phase focuses on documentation. Clear reports explain vulnerabilities, risk severity, evidence, and remediation steps. This phase delivers the most value to organizations.
Types of Ethical Hacking
It can be applied across different technology layers.
Network EthicalHacking
Focuses on routers, switches, firewalls, and network protocols to identify misconfigurations and weak access controls.
Web Application EthicalHacking
Targets websites, APIs, and backend systems to uncover issues such as injection flaws, authentication weaknesses, and insecure session handling.
System EthicalHacking
Examines operating systems, patch levels, and local security controls on servers and endpoints.
Wireless EthicalHacking
Evaluates Wi-Fi encryption, access points, and rogue devices.
Cloud EthicalHacking
Assesses cloud identity management, storage permissions, container security, and shared-responsibility gaps.
Common Tools Used in Ethical Hacking
It relies on professional tools combined with deep technical understanding.
Typical tool categories include:
- Network discovery and scanning tools
- Vulnerability assessment platforms
- Web application testing proxies
- Exploitation and payload frameworks
- Password auditing and credential testing tools
Tools accelerate testing, but ethicalhacking success depends on knowledge, methodology, and responsible usage.
Skills Required to Succeed in Ethical Hacking
A strong ethicalhacking professional develops a balanced skill set.
Technical Foundations
- Networking concepts (TCP/IP, DNS, HTTP)
- Linux and Windows system administration
- Web technologies and APIs
- Basic scripting and automation
Security Expertise
- Vulnerability classes and attack vectors
- Secure configuration standards
- Threat modeling and risk assessment
Professional Skills
- Clear technical reporting
- Communication with non-technical stakeholders
- Ethical decision-making and compliance awareness
This combination of skills is why structured cyber security training is essential for ethical hacking roles.
Ethical Hacking and CEH Certification
The Certified Ethical Hacker (CEH) credential is one of the most widely recognized certifications in this domain. It validates foundational knowledge of ethicalhacking techniques, attack methodologies, and legal considerations.
CEH certification emphasizes understanding attacker behavior, defensive strategies, and structured testing approaches rather than simple tool usage.
Career Roles That Use Ethical Hacking
It skills are applied across multiple cybersecurity roles, including:
- Ethical Hacker
- Penetration Tester
- Cyber Security Analyst
- SOC Analyst
- Security Consultant
These roles rely on ethicalhacking to continuously assess and improve organizational security posture.
EthicalHacking in Enterprise and Industry Environments
Large organizations integrate ethicalhacking into ongoing security programs.
Examples include:
- Regular penetration testing schedules
- Continuous vulnerability management
- Secure development lifecycle testing
- Compliance-driven security assessments
It helps ensure that security controls evolve alongside technology changes.
EthicalHacking in Cybersecurity Training Programs
Modern cybersecurity education emphasizes practical, hands-on learning. Ethicalhacking labs expose learners to real attack scenarios, helping them understand how vulnerabilities are discovered and exploited.
Cyber security training that includes ethicalhacking prepares learners for real job responsibilities, not just theoretical exams.
EthicalHacking and Job Placement Readiness
Employers value candidates who can demonstrate applied skills. Ethicalhacking experience shows that a professional can:
- Identify and validate security weaknesses
- Explain technical risks clearly
- Recommend realistic remediation steps
This is why cyber security training and placement programs often place strong emphasis on ethicalhacking modules and real-world projects.
Legal and Ethical Considerations
Ethicalhacking is strictly regulated. Professionals must always operate within:
- Written authorization and contracts
- Defined scope and boundaries
- Responsible disclosure practices
- Local and international cybersecurity laws
Without these safeguards, activities become illegal regardless of intent.
The Future of EthicalHacking
Ethicalhacking continues to evolve with emerging technologies.
Key trends include:
- AI-assisted vulnerability discovery
- Cloud-native and container security testing
- Integration with DevSecOps pipelines
- Continuous security validation models
Ethicalhacking will increasingly combine automation with human expertise to address large-scale, dynamic environments.
Who Should Learn EthicalHacking?
Ethicalhacking is suitable for a wide range of learners:
- IT professionals transitioning into cybersecurity
- QA professionals expanding into security testing
- Network and system administrators
- Beginners aiming for cybersecurity analyst roles
With structured Cyber security analyst training online, ethicalhacking becomes an accessible and scalable career pathway.
Key Benefits of EthicalHacking Skills
- Proactive risk identification
- Improved security posture
- Enhanced career opportunities
- Better understanding of attacker behavior
- Strong foundation for advanced cybersecurity roles
Key Takeaways
- Ethicalhacking is authorized security testing with defensive intent
- It plays a central role in modern cybersecurity strategies
- Hands-on practice is critical for real-world readiness
- Ethicalhacking supports multiple high-demand career paths
- Structured training improves employability and confidence
Conclusion
As digital systems continue to expand and cyber threats grow more advanced, ethicalhacking remains one of the most effective methods for validating security defenses. It bridges the gap between theoretical controls and real-world attacker behavior, making it an indispensable skill for today’s cybersecurity professionals.