If you’re trying to figure out what real-time scenarios are actually covered in cyber security courses at H2K Infosys, here’s the simple truth: it’s not just theory or slides. The focus is very much on hands-on, job-like situations the kind you’d run into in a SOC (Security Operations Center) or while working as a security analyst.
That might sound like a small detail, but it really isn’t.
Let me walk you through what that actually looks like in practice.
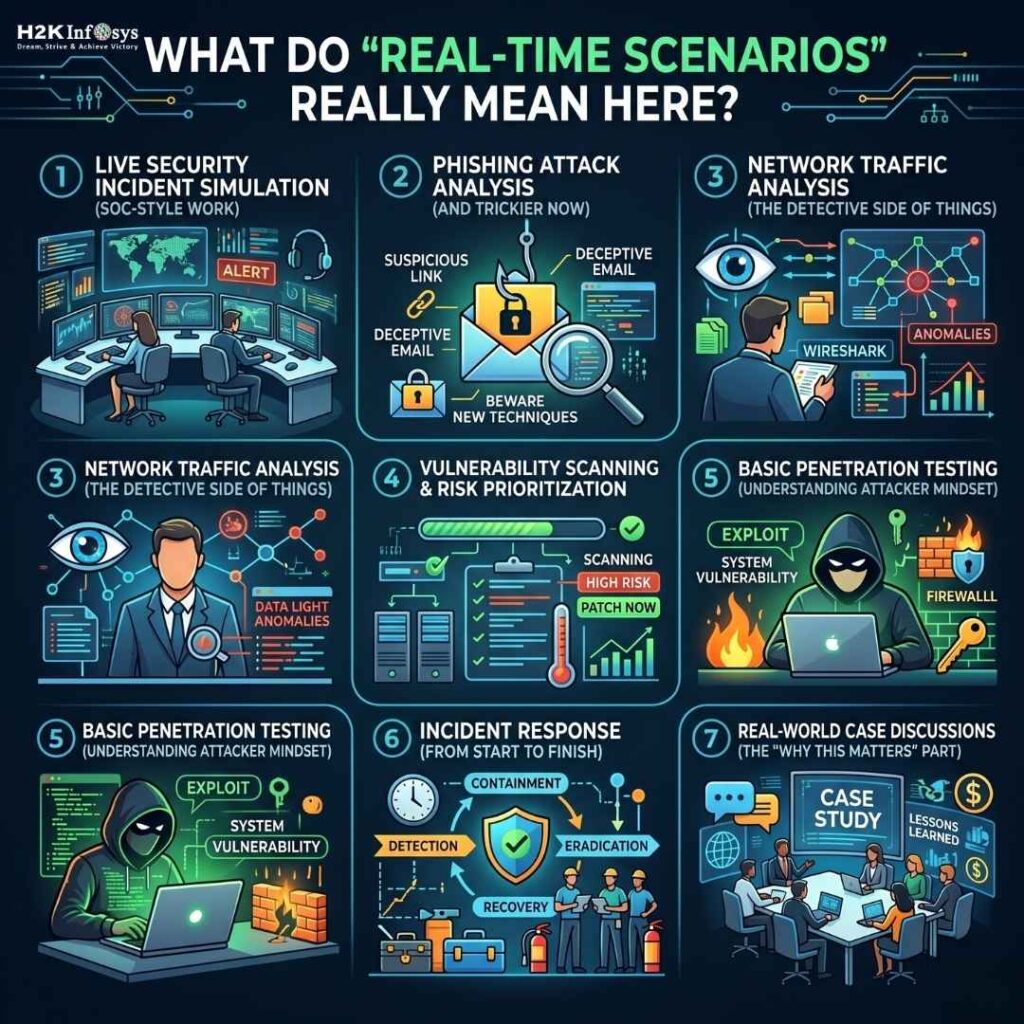
So, what do “real-time scenarios” really mean here?
A lot of people hear cyber security training with job placement and assume it’s mostly about learning tools, maybe passing a certification or two, and calling it a day. I used to think the same, honestly.
But programs like H2K Infosys take a different route. The training feels less like a classroom and more like a controlled version of a real work environment.
You’re not just told, “This is a threat.”
You’re put in a situation where something feels off and now you have to figure out what’s going on.
That shift… it changes how you think.
1. Live Security Incident Simulation (SOC-style work)
One of the first things you’ll deal with is simulated alerts the kind cyber security courses analysts see every single day.
Say you get a login alert from an unusual location.
Not obviously malicious, but definitely not normal either.
Now what?
You’ll:
- Dig through logs using SIEM tools like Splunk
- Correlate activity across systems
- Try to piece together whether it’s harmless or something bigger
It’s not spoon-fed. You actually have to decide. And that’s where a lot of cyber security courses jobs with training programs fall short but here, it’s kind of the core of the learning.
2. Phishing Attack Analysis (and yeah, it’s trickier now)
Phishing used to be easy to spot. Bad grammar, weird links, you know the type.
Not anymore.
With AI-generated emails becoming way more convincing in 2025–2026, even experienced users hesitate sometimes. Training reflects that reality in cyber security courses.
You’ll go through:
- Suspicious emails that look almost legit
- Header analysis
- Link inspection
- Figuring out what’s actually malicious
And somewhere in the middle of it, there’s usually that thought
“Wait… I might’ve clicked this.”
That’s when it clicks (no pun intended).
3. Network Traffic Analysis (the detective side of things)
This part can feel a bit intense at first, not going to lie. But if you like digging into details, it gets interesting fast.
Using tools like Wireshark, you’ll:
- Capture packets
- Look for patterns that don’t quite add up
- Spot potential data leaks or strange communications
It’s less about memorizing commands and more about reading between the lines… or packets, in this case.
4. Vulnerability Scanning & Risk Prioritization
Another big piece is figuring out where systems are weak before someone else does.
You’ll simulate:
- Running scans using tools like Nessus
- Going through long, sometimes overwhelming reports
- Deciding what actually matters vs. what can wait
And yeah, at first everything looks critical. Over time, you start to prioritize better, which is a skill on its own.
5. Basic Penetration Testing (understanding the attacker mindset)
You’re not being trained as a full-blown ethical hacker here, but you do get a glimpse into how attacks happen.
In controlled labs, you might:
- Use tools like Metasploit
- Try exploiting simple vulnerabilities
- See how small gaps can lead to bigger problems
It’s one thing to hear about vulnerabilities. It’s another to actually use one and see what happens.
6. Incident Response (from start to finish)
This is probably one of the more valuable parts of cyber security training and job placement programs like H2K Infosys.
Instead of isolated exercises, you go through the entire process:
- Detection
- Analysis
- Containment
- Eradication
- Recovery
And it’s not always neat. Sometimes you go down the wrong path, backtrack, rethink. Which, to be fair, is exactly how real incidents play out.
7. Real-world case discussions (the “why this matters” part)
Good training doesn’t exist in a bubble.
You’ll look at actual incidents, ransomware attacks, cloud misconfigurations, data breaches and break them down.
What went wrong?
Could it have been avoided?
Where did the process fail?
And honestly, this part sticks with you. It connects everything else you’re learning to what’s actually happening out there right now.
Why this kind of training works (from a practical angle)
If you ask me, the biggest gap in cyber security courses isn’t lack of knowledge, it’s hesitation.
People know concepts, maybe even tools… but when something real shows up, there’s uncertainty. That pause.
Scenario-based training reduces that.
H2K Infosys seems to lean into this idea by mixing:
- Hands-on labs
- Realistic simulations
- Tool-based practice
- And actual job placement support
So when you say you’ve done cyber security courses training with job placement, you’re not just repeating a line. You can actually explain what you did, how you investigated alerts, what decisions you made, where things got confusing.
That’s the stuff interviewers usually dig into.
Final thought (just being honest here)
If you’re serious about getting into cybersecurity jobs with training, try not to get pulled in by courses that are all theory and certifications.
Look for something that makes you think a bit harder. Maybe even feel slightly stuck at times.
That’s usually where the real learning happens.
And that’s pretty much what these real-time scenarios at H2K Infosys are designed to do prepare you for situations that don’t come with clear answers in cyber security courses. In a field that keeps evolving, that kind of experience… It goes a long way.