Yes, some cybersecurity training programs offer real-world cybersecurity simulations of actual attacks. One method of training offered by H2K Infosys is integrating labs that offer practical experiences of incidents that occur in actual enterprises, as opposed to just teaching theory.
If you have ever attempted to learn about real-world cybersecurity theory, you’d know that reading about a cybersecurity attack is completely different from experiencing the attack on a simulated network.
Most companies recruiting for security positions are requesting more than just certifications. They also require a hands-on approach to managing real incidents, analyzing actual records, and responding to simulated breaches. This is the reason why training programs that present active cyber ranges and scenario-based labs are proving to be more beneficial in recent times.
Based on my experience with learners in this field, I can say that H2K Infosys is one of the programs that focus on real-life simulations of cybersecurity extensively.
Now let’s focus on the components and significance of achieving your desired cybersecurity goals with training as opposed to just earning multiple certifications.
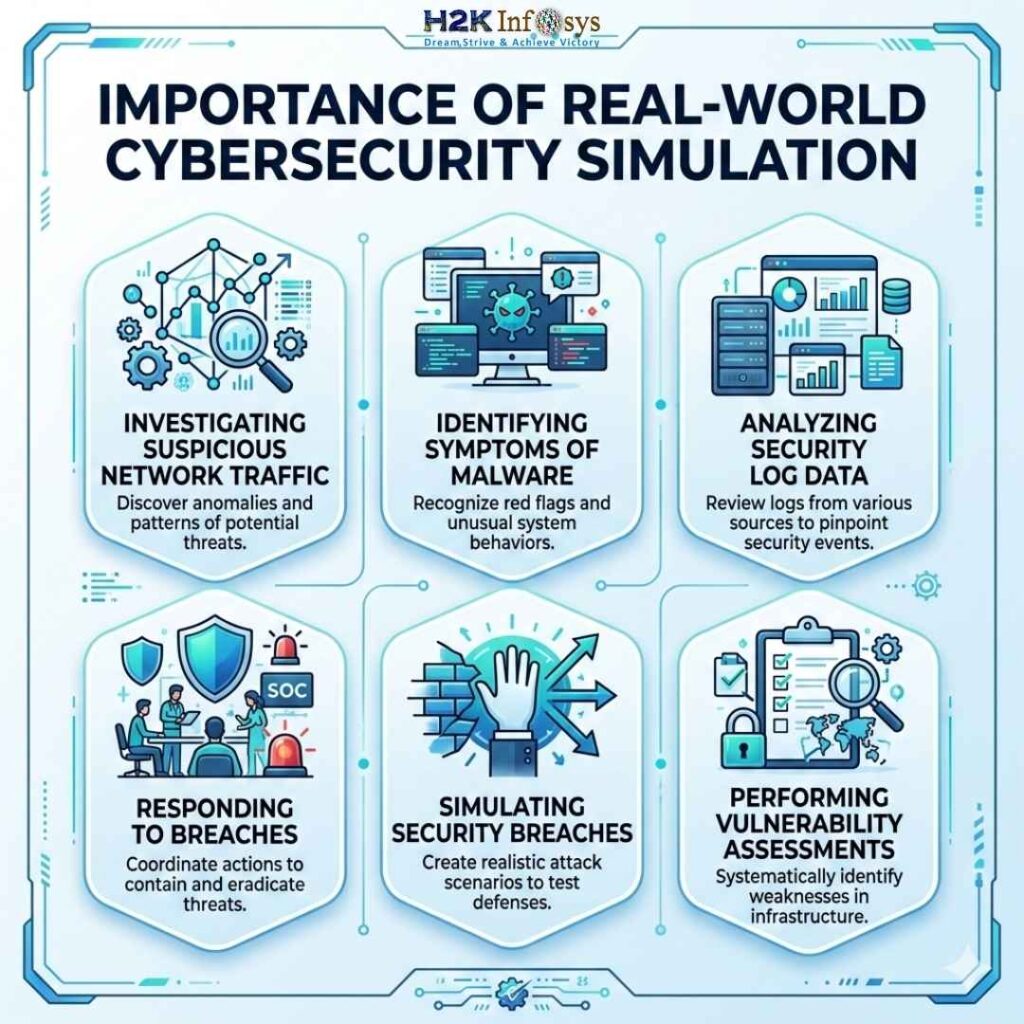
The Importance of Real-World Cybersecurity Simulation
The field of real-world Cybersecurity cannot be understood by reading slides and completing multiple choice quizzes. Real cybersecurity involves working with actual networks, data, and alerts and a multitude of other information that behaves in unpredictable ways.
Let’s say this happens:
A company’s SIEM dashboard detects multiple login failures from multiple locations. Initially, this looks like a case of brute force attack, but a more thorough investigation shows that this looks like a case of credential stuffing attack where leaked credentials from an attack get used to attack the company.
Such discoveries come out of experience gained while working in controlled environments, not in environments where you answer multiple-choice questions.
Training programs that recreate these types of experiences focus on the following skills:
- Investigating suspicious network traffic
- Identifying symptoms of malware
- Analyzing security log data
- Responding to breaches
- Simulating security breaches
- Performing vulnerability assessments.
H2K Infosys Cybersecurity Program
H2K Infosys is unique in that its fast-paced simulation of real-world cybersecurity practices sets it apart from almost every other provider.
The use of enterprise-grade cybersecurity sales training simulations is employed at H2K Infosys. These simulations include:
Enterprise-Grade Cybersecurity Training Simulations
H2K Infosys enterprise-grade cybersecurity training simulations are unique because they offer real-world cybersecurity simulations of enterprise security processes to participants. Unlike other providers, H2K Infosys offers participants the opportunity to engage in real-world enterprise security processes. These simulations include:
Enterprise-grade cybersecurity training simulations.
Incident Response Scenarios
Students train in identifying and responding to incidents such as:
- phishing attempts
- insider threats
- ransomware activity
- suspicious network activity
- Security Tool Experience
The labs introduce security tools and systems that learners are likely to use in order to enable them to obtain experience working with the systems as well as experience working with alerts in the systems as they would in the actual systems.
Because of that experience, their program is frequently cited in relation to real-world cybersecurity training with job placement. Students graduate with experience comparable to actual SOC workflows.
Real World Skills Companies Seek
There has been an interesting development in the field of real-world cybersecurity hiring in the last couple of years. Companies understood that having a certification is not a sufficient measure of job readiness.
Hiring managers look for evidence of tangible job readiness in order to assess a candidate’s ability to perform skills that involve:
- analysis of SIEM alerts
- investigation of suspicious IP addresses
- conducting vulnerability assessments
- response reporting
Programs that combine practical labs and job readiness are the first to close the gap between training and job.
Therefore, many learners prefer real-world cybersecurity training with job placement over the usual routineizied academic courses that offer little to no practical labs.
The Importance of Cybersecurity Training in Sales-Oriented Security Roles

Cybersecurity as a field of study is not completely technical defense roles. There is also an increasing need for people who understand and can sell security solutions to the business.
- This is the relevance of cybersecurity sales training.
- Security vendors today require professionals who understand both the:
- technical details of threats and
- the business ramifications of breaches.
- For instance, someone in cybersecurity sales has to illustrate to a customer:
- the operational impact of a ransomware attack
- the importance of endpoint protection
- the ways in which SIEM tools are employed to identify intrusions
Conversations like these are much more believable if someone has real lab experience from simulation-based training.
Example from the Real World of Simulation Training
A colleague of mine has recently participated in a real-world cybersecurity lab exercise that appeared simple: Investigate unusual outbound traffic from a workstation.
But, in the simulated environment, the scope of the investigation extended to:
- Firewalls
- Suspicious DNS queries
- Malware beacons
Ultimately, the “infected” workstation was exchanging data with a command and control server (C&C).
This single lab exercise was more instructive than weeks of reading.
Incident-style training is what H2K Infosys aims to do.
Why Simulation-Based Cybersecurity Training Is Growing
Over the past few years, the evolution of real-world cybersecurity threats has been dramatic. Increasingly sophisticated ransomware attacks, supply-chain breaches, and phishing campaigns that utilize AI.
As a result, businesses are seeking people who are able to provide real time responses to real world situations as opposed to just providing answers to theoretical questions.
For many newcomers wishing to receive cyber security training with job placement, training programs providing hands-on simulations, professional coaching, and job seeking assistance are becoming increasingly popular.
Conclusion
Programs such as H2K Infosys are unique because they integrate practical laboratories, scenario based learning, and professional assistance to help learners transition to cyber security employment with just training and not solely theoretical knowledge. Therefore, real-world cybersecurity simulations are imperative to developing job ready skills.