The latest cyber threats discussed in cyber security courses at H2K Infosys go far beyond the usual textbook topics most people expect. Students are learning about AI-driven phishing attacks, ransomware-as-a-service (RaaS), cloud security breaches, deepfake scams, insider threats, identity-focused attacks, and even real-time SOC incident response situations that mirror what security teams deal with every day.
What actually makes the training interesting, though, is the hands-on side of it. Learners don’t just sit through theory sessions or memorize definitions for exams. They spend time working through detection scenarios, analyzing alerts, and understanding how these attacks play out inside environments that feel surprisingly close to real-world security operations centers. That practical exposure changes everything for a lot of students.
And honestly, that matters more now than it did even a couple years ago.
A lot of traditional programs still teach cyber threats in a very outdated way, mostly static attack models, old breach examples, and endless PowerPoint slides. The cybersecurity hiring market in 2026 doesn’t really reward that anymore. Companies are looking for people who understand how modern attackers behave, especially in cloud environments where threats evolve fast and rarely follow a predictable pattern.
Cyber Threats Are Changing Faster Than Most People Expect
One thing I’ve personally noticed while following recent SOC reports and breach investigations is how quickly attackers adapt. Security teams barely adjust to one threat pattern before another variation appears.
A few years ago, phishing emails were easy to spot because they looked suspicious. Today? Some AI-generated phishing campaigns are almost indistinguishable from legitimate company communication. Attackers now use generative AI tools to mimic writing styles, create fake login portals, and even automate social engineering conversations.
That shift is heavily discussed inside modern cyber security training with job placement programs because recruiters expect candidates to understand these evolving attack patterns before entering interviews.
At H2K Infosys, students are introduced to threat detection methods that reflect what analysts actually encounter inside enterprise environments.
AI-Powered Phishing Attacks Are a Huge Focus
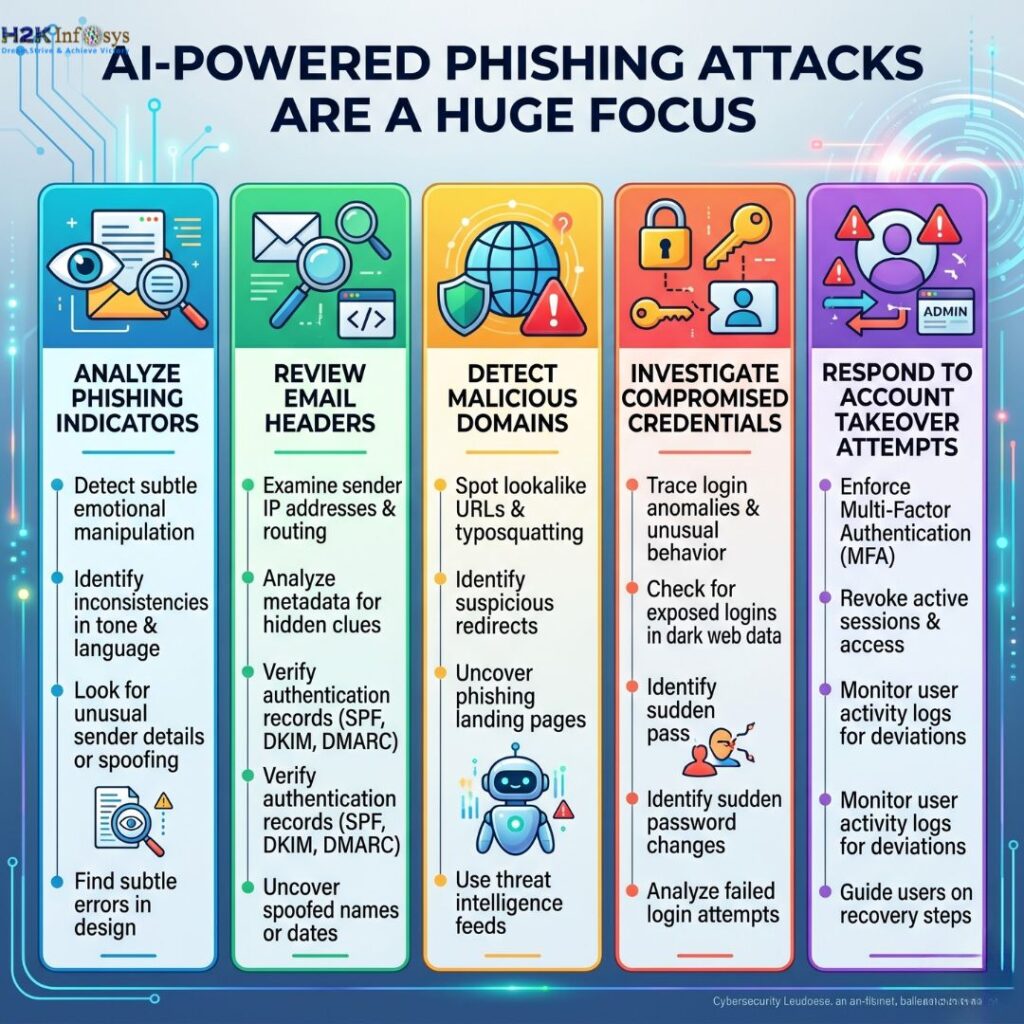
Honestly, this is probably one of the biggest topics in cyber security courses training right now.
Attackers increasingly use AI to:
- Generate convincing phishing emails
- Clone writing styles from executives
- Create fake support chats
- Launch credential harvesting attacks
- Automate spear-phishing campaigns
In real-world SOC environments, analysts now spend significant time investigating suspicious login activity tied to phishing campaigns.
Students in cyber security training and job placement programs learn how to:
- Analyze phishing indicators
- Review email headers
- Detect malicious domains
- Investigate compromised credentials
- Respond to account takeover attempts
That practical exposure helps learners understand how attacks unfold beyond theory. And honestly, interviewers notice the difference pretty quickly when candidates can explain actual investigation workflows.
Ransomware-as-a-Service (RaaS) Is Now an Everyday Threat
Ransomware used to feel like something only huge corporations worried about.
Not anymore.
Hospitals, schools, financial firms, and even small businesses are constantly targeted now. Attackers no longer need advanced coding expertise because ransomware kits are sold through underground marketplaces as subscription services.
That’s why cyber security jobs with training increasingly require familiarity with ransomware behavior analysis.
Inside practical labs, learners often explore scenarios involving:
- Suspicious file encryption activity
- Endpoint compromise alerts
- Lateral movement detection
- SIEM investigation workflows
- Incident escalation procedures
Many students entering cybersecurity from non-IT backgrounds initially find these concepts intimidating. But hands-on practice changes that pretty fast. Once learners begin working through realistic SOC alerts, things start making more sense in context.
Cloud Security Threats Are Discussed Much More in 2026
Cloud environments are now one of the biggest attack surfaces in cybersecurity.
A surprising number of breaches happen because of:
- Misconfigured cloud storage
- Weak IAM permissions
- Exposed APIs
- Poor identity management
- Insecure multi-cloud environments
This is why modern cyber security training with job placement programs spend much more time on AWS security fundamentals, cloud monitoring, and identity protection.
At H2K Infosys, students are exposed to practical cloud-security-related scenarios that align more closely with current hiring demands. Employers increasingly expect entry-level analysts to understand at least the basics of cloud attack detection.
That wasn’t always true a few years ago.
Deepfake Scams and Identity-Based Attacks Are Growing Fast
This trend became especially alarming during late 2025 and early 2026.
Cybercriminals now use deepfake audio and AI-generated video impersonation to manipulate employees into approving payments or sharing credentials. Some attacks imitate executives during virtual meetings or voicemail messages.
Honestly, it sounds futuristic until you see real cases.
Training programs focused on cyber security jobs with training now discuss how attackers combine:
- Social engineering
- Identity compromise
- MFA fatigue attacks
- Deepfake impersonation
- AI-generated voice cloning
Security awareness alone isn’t enough anymore. Analysts must understand behavioral anomalies and authentication monitoring techniques.
That’s why practical SOC-style learning environments matter so much.
Insider Threats Are Still One of the Hardest Risks to Detect
Interestingly, not every cyber threat comes from outside attackers.
Sometimes the danger comes from employees, contractors, or privileged users misusing access intentionally or accidentally.
Modern cyber security training and job placement programs now teach students how SOC teams monitor:
- Abnormal login patterns
- Unauthorized data transfers
- Privilege escalation activity
- Unusual endpoint behavior
- Sensitive file access anomalies
These are real-world detection scenarios security analysts handle daily.
I’ve noticed many learners initially assume cyber security courses is mostly “hacking defense,” but a huge portion of real analyst work actually involves log analysis, behavior monitoring, and incident triage.
SIEM and Threat Monitoring Are Central to Modern Training
This is probably where many students gain the most confidence.
Instead of only memorizing concepts, learners inside strong cyber security courses training with job placement programs spend time working with:
- SIEM dashboards
- Security alerts
- Threat intelligence feeds
- Log correlation tools
- Incident response workflows
At H2K Infosys, practical exposure is designed to reflect actual SOC analyst responsibilities. That hands-on structure helps bridge the gap between classroom learning and real job expectations.
And honestly, employers care about that gap a lot now.
Certificates alone rarely guarantee interviews anymore.
Why Employers Prefer Candidates Who Understand Current Threats
The cyber security courses industry has become much more practical-focused over the last couple of years.
Recruiters now ask questions like:
- How would you investigate suspicious login attempts?
- What steps would you take during a ransomware alert?
- How do phishing attacks bypass MFA?
- What indicators suggest lateral movement?
Candidates who completed hands-on cyber security jobs with training programs usually perform better during these discussions because they’ve already worked through simulated attack scenarios.
That’s one reason programs emphasizing real-world exposure continue gaining attention in the U.S. job market.
H2K Infosys Focuses on Realistic Security Scenarios
One thing many learners appreciate about H2K Infosys is the emphasis on practical cyber security courses workflows rather than only certification preparation.
Students often gain exposure to:
- SOC analyst activities
- Real-time alert analysis
- Incident investigation practices
- Cloud security basics
- Threat monitoring techniques
- Interview preparation support
For career changers, that structure can make the transition into IT feel more manageable.
Especially for beginners, learning through realistic attack simulations tends to build confidence much faster than passive video lectures alone.
Final Thoughts
Cyber threats in 2026 are more AI-driven, identity-focused, and cloud-centered than ever before. Because of that, cyber security courses education has also evolved. The best cyber security training and job placement programs now focus heavily on practical threat detection, ransomware response, phishing investigations, SIEM monitoring, and cloud security awareness.
H2K Infosys discusses many of these modern threats inside hands-on training environments designed to mirror real workplace scenarios. For students trying to break into cybersecurity careers, that kind of practical exposure can make a significant difference when applying for entry-level analyst and SOC roles in today’s competitive hiring market.