Introduction
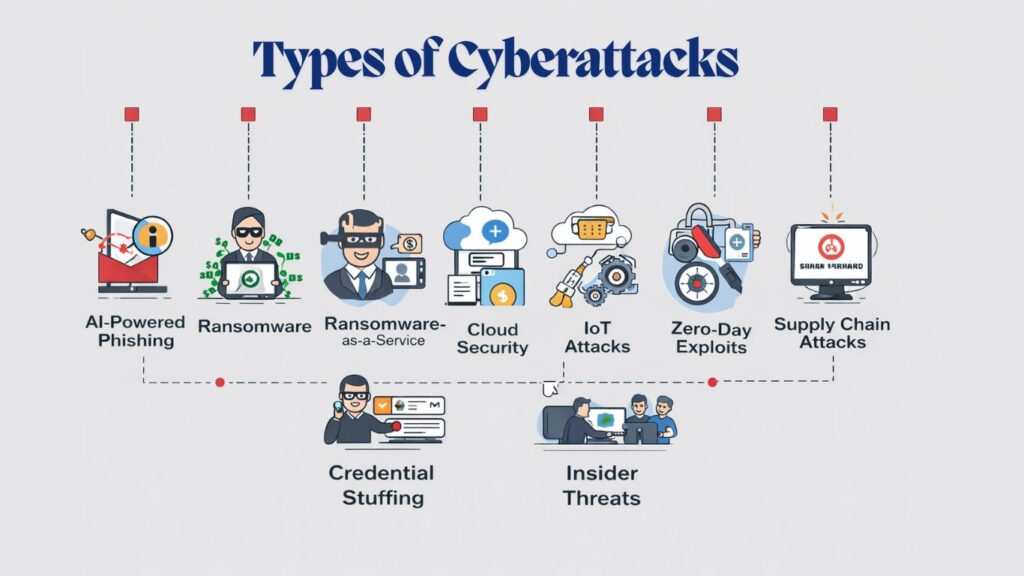
As technology continues to evolve, cyber threats are becoming more advanced and harder to detect. H2K Infosys is one of the platforms that many learners explore to gain practical cybersecurity skills and stay ahead of modern risks. Understanding the Top Cyber Attack Types is essential for businesses and individuals who want to protect their data and systems in 2026.
With organizations rapidly adopting digital transformation, attackers are leveraging artificial intelligence, automation, and human psychology to exploit vulnerabilities. This makes awareness of the Top Cyber Attack Types more important than ever. Many professionals today are enrolling in Cyber security online training and choosing a cyber security course with placement to build skills that can defend against these evolving threats.
AI-Powered Phishing Attacks
One of the most dangerous entries among the Top Cyber Attack Types is AI-powered phishing. Traditional phishing emails were easier to detect due to poor grammar and generic messaging. However, in 2026, attackers use artificial intelligence to craft highly personalized and convincing messages.
These emails often mimic real conversations, include accurate personal details, and appear to come from trusted sources. AI tools analyze social media and public data to create targeted attacks that are difficult to identify. As a result, phishing remains one of the Top Cyber Attack Types affecting both individuals and organizations.
Cyber security online training programs teach learners how to detect subtle phishing indicators and implement preventive measures like multi-factor authentication and email filtering.
Ransomware-as-a-Service (RaaS)
Ransomware continues to dominate the list of Top Cyber Attack Types, but its evolution into Ransomware-as-a-Service has made it even more dangerous. In this model, cybercriminals sell ransomware tools to others, allowing even non-technical attackers to launch sophisticated attacks.
In 2026, ransomware attacks are more targeted and often involve double extortion. Attackers not only encrypt data but also threaten to release sensitive information if the ransom is not paid. This tactic makes ransomware one of the most impactful Top Cyber Attack Types in today’s digital landscape.
A cyber security course with placement helps learners understand how ransomware works and how to respond effectively during such incidents.
Deepfake and Social Engineering Attacks
Deepfake technology has transformed social engineering into one of the most deceptive Top Cyber Attack Types. Attackers can now create realistic audio and video impersonations of executives or trusted individuals.
For example, an employee might receive a video call that appears to be from their CEO, instructing them to transfer funds urgently. These attacks exploit trust and authority, making them highly effective. This is why deepfake-based scams are rapidly rising among the Top Cyber Attack Types in 2026.
Cyber security online training emphasizes verification processes and employee awareness to combat such threats.
Cloud Security Attacks
As companies move their operations to the cloud, cloud-based threats have become a major concern. Misconfigured settings, weak access controls, and insecure APIs make cloud environments vulnerable.
Cloud attacks are now firmly established among the Top Cyber Attack Types because they can expose massive amounts of sensitive data. Attackers often target poorly secured storage systems or hijack accounts to gain unauthorized access.
Professionals taking a cyber security course with placement learn how to secure cloud environments using encryption, identity management, and monitoring tools.
Internet of Things (IoT) Attacks
The rapid growth of connected devices has introduced new vulnerabilities. Many IoT devices lack proper security features, making them easy targets for attackers.
IoT-based threats are increasingly recognized as one of the Top Cyber Attack Types because they can be used to launch large-scale attacks like botnets or DDoS campaigns. A single compromised device can provide entry into an entire network.
Cyber security online training helps learners understand how to secure IoT ecosystems through device authentication and network segmentation.
Zero-Day Exploits
Zero-day vulnerabilities are among the most critical Top Cyber Attack Types because they exploit unknown flaws in software. Since these vulnerabilities are not yet patched, attackers can use them to infiltrate systems without detection.
In 2026, zero-day attacks are becoming more frequent and are often used in targeted operations against high-value organizations. Their unpredictable nature makes them one of the most dangerous Top Cyber Attack Types.
A cyber security course with placement equips learners with skills in threat detection and vulnerability management to address such risks.
Supply Chain Attacks
Supply chain attacks have emerged as one of the most complex Top Cyber Attack Types. Instead of targeting a company directly, attackers infiltrate third-party vendors to gain access to larger systems.
These attacks can spread across multiple organizations, causing widespread damage. Because they originate from trusted sources, they are difficult to detect and mitigate.
Cyber security online training teaches how to assess vendor risks and implement strong third-party security policies.
Distributed Denial-of-Service (DDoS) Attacks
DDoS attacks continue to be a major threat in 2026. By overwhelming systems with massive traffic, attackers can disrupt services and cause downtime.
DDoS attacks remain one of the most disruptive Top Cyber Attack Types, especially for businesses that rely on online platforms. Modern attacks are more targeted and can focus on specific applications rather than entire networks.
Learners in a cyber security course with placement gain practical knowledge of DDoS mitigation techniques such as traffic filtering and load balancing.
Credential Stuffing Attacks
Credential stuffing is a growing concern due to widespread password reuse. Attackers use stolen credentials from previous breaches to access accounts on multiple platforms.
This method has become one of the most common Top Cyber Attack Types because of its simplicity and effectiveness. Automated tools allow attackers to test millions of login combinations quickly.
Cyber security online training focuses on strengthening authentication systems and promoting secure password practices.
Insider Threats
Insider threats are often overlooked but remain one of the most serious Top Cyber Attack Types. These threats come from individuals within an organization who misuse their access.
In 2026, remote work has increased the risk of insider attacks. Employees may intentionally or unintentionally expose sensitive data, leading to breaches.
A cyber security course with placement highlights the importance of monitoring, access control, and employee training to reduce insider risks.
Preparing for the Future
Understanding the Top Cyber Attack Types is essential for staying secure in a rapidly evolving digital world. Organizations must adopt a proactive approach by investing in advanced security tools and educating their workforce.
For individuals, cyber security online training provides the foundation needed to identify and prevent attacks. These programs include real-world scenarios that prepare learners for actual challenges in the field.
Enrolling in a cyber security course with placement not only builds technical expertise but also offers career support, helping learners secure roles in cybersecurity.
Conclusion
The rise of sophisticated threats makes it crucial to stay informed about the Top Cyber Attack Types in 2026. From AI-powered phishing to ransomware and deepfake attacks, cybercriminals are constantly evolving their strategies.
By understanding the Top Cyber Attack Types and implementing strong security measures, organizations can reduce risks and protect their digital assets. At the same time, individuals can take advantage of cyber security online training to build in-demand skills. Choosing a Cyber security course with placement can open doors to rewarding career opportunities while equipping learners with the knowledge needed to combat modern cyber threats.