If you join cyber security training at H2K Infosys, you’ll end up mastering a practical stack of tools used by real security teams think SIEM platforms like Splunk, network analyzers like Wireshark, cloud security basics, threat detection workflows, and hands-on incident response skills that actually translate into a job.
What You’ll Actually Learn (Not Just Theory)
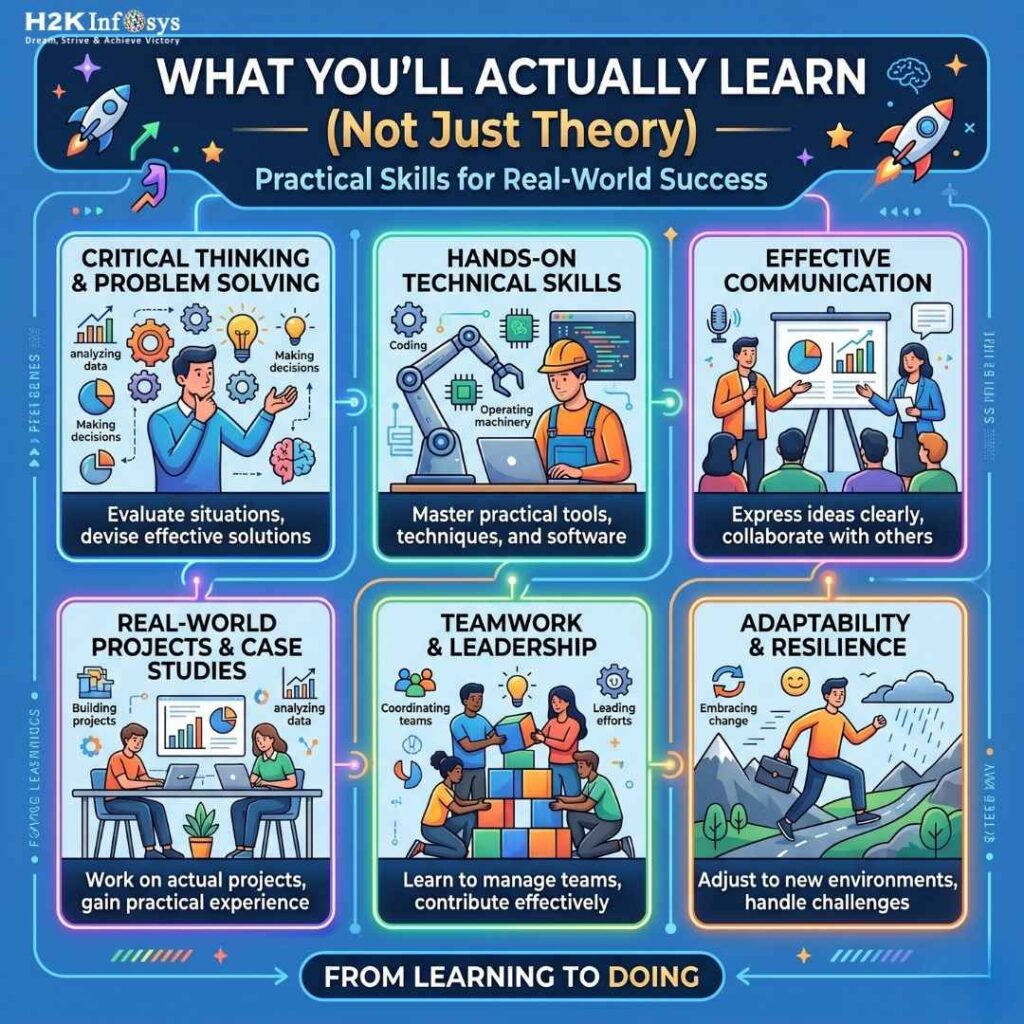
One thing I’ve noticed after going through different training programs and speaking with people already working in SOC teams: tools matter more than slides. You can read about threats all day, but until you open a dashboard and investigate a real alert, it doesn’t click.
That’s where cyber security training with job placement programs stand out. At H2K Infosys, the focus leans heavily toward doing the work, not just understanding it.
Here’s how that breaks down.
SIEM Tools – Where Security Analysts Spend Most of Their Time
You’ll spend a good chunk of training working with Splunk, which honestly is a must-have skill right now. Many companies in the US still rely on SIEM tools to monitor logs and detect suspicious activity.
Instead of just learning commands, you actually:
- Analyze real-time logs
- Create alerts
- Investigate suspicious login attempts
I remember someone mentioning how they were asked in an interview to explain a Splunk dashboard they built not just what Splunk is. That’s the difference hands-on training makes.
Network Security Tools – Understanding What’s Really Happening
Then comes tools like Wireshark.
At first, it can feel overwhelming, tons of packets flying everywhere. At first, it honestly feels a bit chaotic packets everywhere, numbers scrolling, nothing making much sense. But give it a little time, and something clicks. You start to “read” network behavior almost like a pattern instead of noise.
You’ll get hands-on with things like:
- capturing packets and actually figuring out what’s inside them
- spotting traffic that just feels… off
- recognizing signs of attacks spoofing, scanning, that kind of activity
And this is where it stops being just a learning exercise. When you’re dealing with real incidents, this skill becomes incredibly useful. You’re not guessing anymore you’re observing, connecting dots, and making decisions based on what you see. That shift is a big one.
Cloud Security Basics – Because Everything Is Moving to the Cloud
You can’t ignore clouds anymore. Most modern infrastructure sits on AWS or Azure, so cyber security training and placement programs now include cloud security fundamentals.
At H2K Infosys, you typically cover:
- Identity and Access Management (IAM)
- Cloud misconfigurations
- Basic threat detection in cloud environments
And honestly, recruiters love seeing even basic cloud exposure. It signals you’re not stuck in outdated systems.
Threat Intelligence & Incident Response
This is where things get interesting.
Instead of just learning definitions, you walk through:
- Real attack scenarios
- Incident response steps
- Threat hunting basics
You start thinking like an analyst:
“Is this normal traffic… or something off?”
That mindset shift is huge.
With cyber security training and job placement, the goal isn’t memorization, it’s decision-making under pressure.
Hands-On Labs & Real-Time Projects
This is probably the biggest advantage.
H2K Infosys structures training around:
- Simulated SOC environments
- Real-world case studies
- Step-by-step investigation exercises
I’ve seen learners say this part helped them more than anything else. Because when you sit in an interview and someone asks,
“Have you worked on a real incident?”
you actually have something to talk about.
Resume, Mock Interviews & Job Support
Let’s be real tools alone won’t get you hired.
That’s why cyber security training and job placement also includes:
- Resume building based on your lab experience
- Mock interviews with real scenarios
- Guidance on how to explain projects confidently
This part is often underrated, but it’s what connects your skills to actual job offers.
Why These Tools Matter in 2026
Cyber security training hiring has shifted a bit recently. Companies aren’t just asking for certifications they want proof you can work with tools.
With increasing ransomware attacks and cloud breaches making headlines even this year, organizations are prioritizing candidates who can:
- Detect threats early
- Respond quickly
- Understand both on-prem and cloud environments
That’s exactly the gap cyber security training and placement programs aim to fill.
Final Thought (From a Practical Perspective)
If you’re expecting just lectures, this kind of training will feel different in a good way.
You’re not just learning cyber security training. You’re practicing the role of a Security Analyst before you even get hired.
And that’s really the point.
Programs like H2K Infosys don’t just teach tools, they help you build job-ready confidence, which, honestly, is what most beginners struggle with the most.