Yes you do get hands-on experience with real industry tools during cyber security training at H2K Infosys, and honestly, that’s one of the biggest reasons people actually feel job-ready by the end of it.
Let me explain this in a way that reflects what actually happens inside a good training program (not just what’s written on course pages).
What “hands-on” really looks like (not just theory)
A lot of courses say they’re practical, but then you log in and it’s mostly slides and recorded lectures. That’s not the case here. In structured cyber security training with job placement, the expectation is that you’ll use the same tools that working analysts use daily, not just hear about them.
For example, instead of reading about cyber security training attacks, you might:
- Investigate simulated security incidents
- Analyze real log files
- Detect suspicious network activity
- Practice responding to breaches in a controlled lab
It feels less like “studying” and more like doing the job in a safe environment.
Tools you’ll actually work with
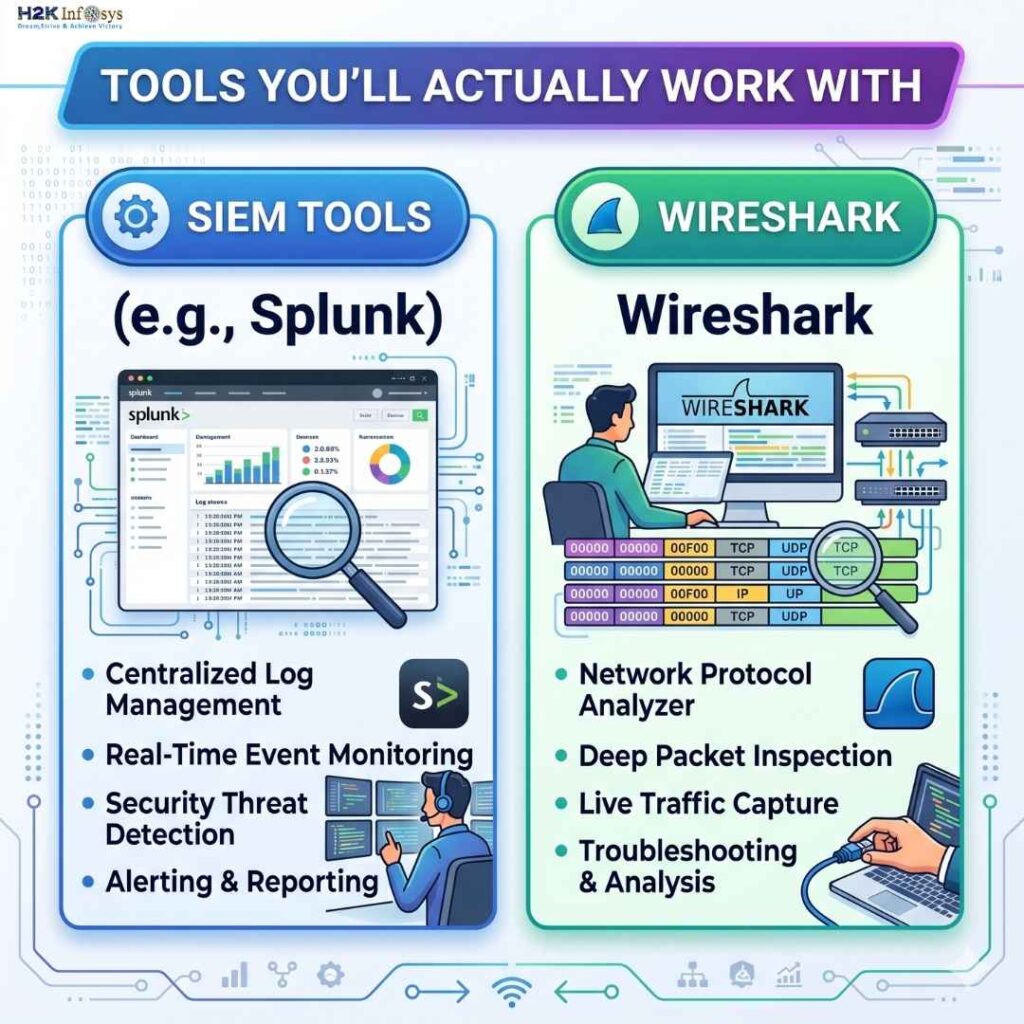
From what I’ve seen in programs like H2K Infosys cyber security training, the tool exposure is very aligned with real job roles. You’re not learning random software,You’re not just picking up random tools here you’re getting familiar with the ones companies are actually hiring for right now. That’s a pretty big difference, and you start to notice it once you look at real job descriptions.
A quick snapshot of what you’ll run into:
- SIEM tools (like Splunk): This is where you’ll spend time digging through logs, spotting weird patterns, figuring out what’s normal and what’s… not. It’s basically how security teams keep an eye on things in real time. Takes a bit to get used to, honestly, but it clicks after a while.
- Wireshark: If you’re even slightly curious about what’s happening under the hood of a network, this one pulls you in. You’re looking at packets, traffic flows kind of like zooming into the internet at a microscopic level. It can feel overwhelming at first, but also weirdly interesting once you get the hang of it.
Real-world scenarios (this is where it clicks)
One thing that stands out and I’ve heard this from quite a few learners is how scenario-based the cyber security training gets.
Instead of:
“Here’s what a phishing attack is…”
You get something like:
“A company’s email server shows unusual login activity. Investigate.”
And suddenly you’re:
- Checking logs
- Tracing IP addresses
- Identifying suspicious patterns
- Writing a basic incident report
That shift from passive learning to active problem-solving is what bridges the gap between learning and actually landing cyber security jobs with training.
How this connects to job readiness
Here’s the uncomfortable truth: many candidates finish courses but still struggle in interviews because they can’t explain what they’ve done.
Hands-on cyber security training changes that.
Instead of saying:
“I learned about SIEM tools…”
You can say:
“I used Splunk to analyze login anomalies and identify brute-force attempts during a simulated incident.”
What’s the difference? Huge.
Programs like H2K Infosys tend to integrate:
- Resume-building based on real lab work
- Mock interviews using practical scenarios
- Guidance on how to explain your hands-on experience
And that’s often what makes cyber security training with job placement actually deliver on its promise.
A quick reality check (worth knowing)
Not every session will feel exciting. Some labs can be messy, confusing, even frustrating at first. Logs don’t always make sense immediately. Tools can feel overwhelming.
But that’s kind of the point.
Because real cyber security training work isn’t clean or predictable either.
Why H2K Infosys stands out here
What I’ve personally noticed is that H2K Infosys leans heavily into job-aligned learning. It’s not just about finishing modules, it’s about making sure you can step into an entry-level role and not feel completely lost on day one.
That includes:
- Guided hands-on labs
- Real-time project exposure
- Tool-based learning (not just concepts)
- Placement-oriented support throughout the journey
And somewhere along the way, you stop asking “Will I get hands-on experience?” and start thinking, “Okay… I can actually do this.”
Final thought
If your goal is to move into cyber security, hands-on experience isn’t optional, it’s the whole game. The right cyber security training and job placement program doesn’t just teach you what cyber security training is; it puts you in situations where you practice it.
And that’s exactly what makes the difference when you start applying for real roles.