Yes,H2K Infosys does include live cyber attack simulations as part of its training, and that’s actually one of the more practical aspects of the program. Instead of just explaining threats in theory, the training walks you through how attacks unfold in real environments step by step, sometimes a bit messy, just like in real life.
So what do “live cyber attack simulations” actually look like?
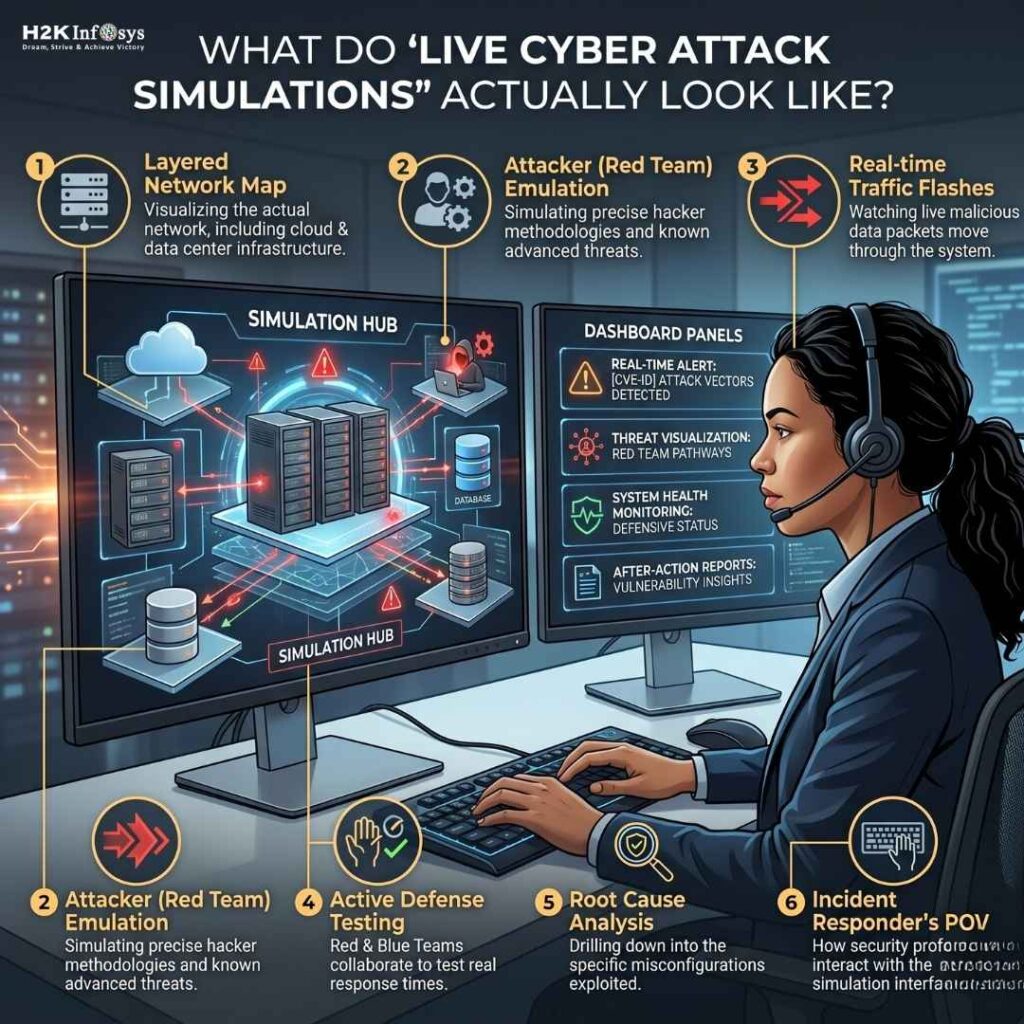
When people hear that phrase, they often imagine something overly complex or reserved for advanced professionals. But from what I’ve seen and honestly, what most learners experience it’s more like controlled chaos inside a safe lab environment.
You’re not just reading about phishing or ransomware. You’re watching it happen.
For example, one common scenario involves a cyber attack simulations phishing attack. You might receive what looks like a normal email, click something you shouldn’t (on purpose), and then trace how that single action leads to credential compromise. From there, you analyze logs, detect anomalies, and figure out how to stop it. It’s simple at first, then it escalates quickly.
That’s where cybersecurity training and placement programs start to feel real because you’re no longer memorizing definitions, you’re reacting.
Why simulations matter more in 2026 than ever
Cybersecurity has changed a lot recently. cyber Attack simulations are no longer slow or manual. They’re automated, often powered by AI, and designed to adapt in real time. You’ll see things like:
- AI-generated phishing emails that sound too human
- Malware that changes behavior to avoid detection
- Automated scanning tools probing systems 24/7
This is exactly why cyber security training and placement programs now emphasize simulations. It’s the only way to prepare for something that doesn’t follow a script.
I remember talking to someone who went through a purely theory-based course. They could explain ransomware perfectly but froze when asked how to respond to an active incident. That gap? cyber attack Simulations fix it.
Where H2K Infosys fits into this
Somewhere in the middle of the training journey, H2K Infosys introduces these simulation-based labs in a way that feels less like “training” and more like a rehearsal for an actual job.
You’ll typically work with tools like:
- SIEM platforms for log analysis
- Network monitoring tools
- Basic penetration testing setups
And then the scenario hits: unusual traffic patterns, login failures, suspicious scripts running in the background.
At that point, it’s on you to investigate.
This is also where cyber security training with job placement support becomes meaningful. Because during interviews, employers don’t just ask “What is a cyber attack?” they ask, “What would you do if you saw this?”
If you’ve already walked through similar cyber attack simulations, your answers come out naturally.
A quick real-world parallel
Think about the ransomware attacks we’ve seen in the last couple of years especially those targeting healthcare and financial systems. These weren’t one-step attacks. They involved:
- Initial access (often phishing)
- Lateral movement inside the network
- Data exfiltration
- Encryption and ransom demand
Good simulations mirror this chain. Not perfectly, but enough to give you that “oh, this is how it actually unfolds” moment.
And once you see that flow even once, it sticks.
Is it beginner-friendly though?
Surprisingly, yes… but with a small caveat.
The early simulations are guided. You’re not thrown into a full-blown attack scenario on day one. But as you progress, the hand-holding reduces. That’s intentional.
There might be moments where you feel slightly stuck. That’s part of the design. Real cybersecurity work isn’t clean or predictable, and good training reflects that.
Final thought
If you’re considering cybersecurity as a career, this is one thing I’d pay close attention to: does the program let you experience attacks, not just study them for cyber attack simulations?
Because reading about threats builds awareness…
But responding to them even in a simulated lab that’s what builds confidence.
And in today’s hiring market, confidence backed by hands-on experience is what really sets candidates apart.