Introduction
If you’re considering taking the plunge into the world of cybersecurity, you’ve probably found that there’s no shortage of cyber security online training programs out there. H2K Infosys knows this challenge better than most and offers programs that bridge the gap between theory and practice.
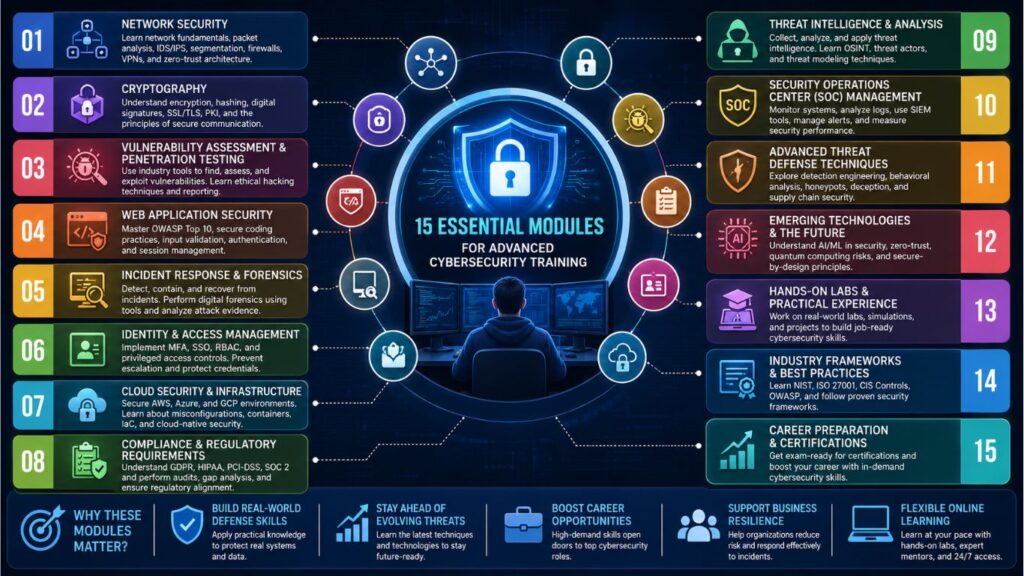
But not all Online courses for cybersecurity are created equal and frankly that’s what makes finding the right program exciting and overwhelming all at the same time. The real question is not just whether you should get trained, but whether the Modules Are Covered in Cybersecurity training you choose actually covers what’s important in the real world.
Understanding the Foundation of Modern Cybersecurity Training
When you begin to look at online training programs for cyber security, you will see they are very different in scope and depth. Some are just shallow introductions, literally. Some get into the technical details. The very best Modules Are Covered in Cybersecurity ? They work against each other.
Advanced cybersecurity training works because it doesn’t just teach you concepts in a vacuum. It shows you how those concepts work in real business environments. It reveals the real mistakes companies make, the real vulnerabilities they miss, and the real strategies that actually stop attackers.
modules are incorporated into cybersecurity training programs built for today’s threat landscape. That landscape is constantly changing. New vulnerabilities keep emerging. From attacker’s perspective social engineering is getting smarter. Cloud security is more important than ever. And the attack surface continues to expand as organizations move more of their operations online.
Network Security Fundamentals and Advanced Topics
Let’s start with network security, because network is the foundation of everything in cyber security. If you don’t understand the Modules Are Covered in Cybersecurity it you can’t protect it.
Network security modules start with the basics how packets move through networks, how TCP/IP works, the OSI model. But the advanced modules are so much more. These include packet analysis, intrusion detection systems and network segmentation techniques. Modules Are Covered in Cybersecurity to help you understand not only how networks work but how to defend them.
One of the practical things you will do is learn Wireshark and related packet analysis tools. You will capture real network traffic and learn to recognize the patterns that indicate something malicious is happening. This isn’t a theory. You are seeing what attacks look like in the wild, for real.
The modules include cybersecurity for students and professionals who need to know how to implement firewalls, configure VLANs and set up network monitoring systems. You learn about zero-trust architecture. The concept Modules Are Covered in Cybersecurity that just because something is inside your network doesn’t mean you should trust it. You understand DDoS attacks from both sides – how they work and how to mitigate them.
Cryptography: The Math Behind Security
This is where a lot of people get scared. However, cyber security online training cryptography Modules Are Covered in Cybersecurity don’t expect you to be a mathematician. They do require you to understand what actually happens when data is encrypted.
You’ll learn about symmetric encryption (same key for encryption and decryption) vs. asymmetric encryption (public and private keys). It is going to show you why AES is still considered secure and DES is completely outdated. Go to a website and see how SSL/TLS works. That is cryptography in action.
Cybersecurity training programs cover the modules to show you how certificates work, what certificate authorities do and why a compromised CA is such a big deal. You’ll learn about hashing, and that hash is not the same thing as encryption. This is significant because security teams often deal with hashed passwords, data integrity checks and digital signatures.
Other topics include quantum computing and cryptographic agility. What happens when quantum computers become practical ? Some of the encryption we use today will break overnight. There are already good training programs out there training people for this reality.
Vulnerability Assessment and Penetration Testing
This is one of the most practical and hands on fields. The modules are covered in cybersecurity training specifically to teach you how to find vulnerabilities before the bad guys do.
Vulnerability Assessment starts with scanning tools like Nessus, OpenVAS and Qualys. You will learn how to run the tools, interpret the results, and prioritize what actually needs to be fixed. But not all vulnerabilities are created equal. A vulnerability on an internal development server is not as urgent as a vulnerability on a customer-facing web app.
The next level is penetration testing. Now, you’re not just finding vulnerabilities, you’re trying to actually exploit them. Of course, this is done legally, with the proper authorization. You learn social engineering tactics because many real attacks are not based on technical vulnerabilities. They depend on people to screw up.
The cybersecurity courses cover modules on methodologies like the NIST Cybersecurity Framework and OWASP’s top 10. These frameworks offer a structured approach for identifying and addressing security risks. You learn how to write compelling penetration test reports that will actually convince management to fix things.
Web Application Security
Today, a lot of the action is happening in web applications. Web applications are everywhere from e-commerce sites to SaaS applications to internal business applications and are often the target of attacks.
In web application security, online training modules in cyber security will teach you about the OWASP Top 10 vulnerabilities. SQL injection, cross site scripting (XSS), cross site request forgery (CSRF) – find out how these attacks work and more importantly how to prevent them. You don’t just learn to find them in existing code. You learn to code securely, immediately.
The Modules Are Covered in Cybersecurity for both developers and security professionals. The truth is, developers and security teams need to speak the same language. If a developer does not understand why they shouldn’t trust user input then any application they build is vulnerable.
You will learn about secure coding practices, input validation, output encoding and parameterized queries. You will learn about authentication and authorization mechanisms You’ll learn why session management is important, and what happens when it does not work properly.
Incident Response and Forensics
So even with your best efforts to prevent incidents, at some point incidents happen. That’s what incident response is for.
The Modules Are Covered in Cybersecurity so you will be prepared for the reality that someday you may be on a team working with a security breach. You’ll learn how to know that a breach is happening, how to contain it, how to get rid of the threat and how to recover.
Forensics is the detective side. You learn how to preserve evidence. How to maintain the chain of custody. How to analyze systems to see what happened. This matters if you’re dealing with a compromised web server or malware on an employee’s laptop.
These Modules Are Covered in Cybersecurity incident response plans, communication protocols, and how to coordinate with executives, legal teams, and law enforcement agencies. Many breaches go from bad to catastrophic because the response was a mess.
You’ll be working with tools like EnCase, Autopsy, Volatility. You will learn memory analysis, disk forensics, and log analysis. These are practical skills that security teams use every day by Modules Are Covered in Cybersecurity.
Identity and Access Management
Identity and access management (IAM) might not sound as sexy as penetration testing, but it is absolutely critical. Many breaches occur because attackers acquire valid credentials.
In cybersecurity training, the Modules Are Covered in Cybersecurity teach you how to implement strong identity and access controls. You learn about multi-factor authentication (MFA) and why a password just isn’t sufficient anymore. You know how single sign-on ( SSO ) systems work and what authentication protocols they use .
You will be introduced to role based access control (RBAC) and attribute based access control (ABAC). It’s a simple idea: people should be given only what they need to do their work. But to do this consistently across an entire organization is difficult.
These modules include priviledge escalation attacks. How do attackers escalate from low privilege account to administrative access? This knowledge can help you to put in place controls to make privilege escalation harder to pull off.
You’ll learn about password policies, credential management and how to detect anomalous access patterns that could indicate a compromise.
Cloud Security and Infrastructure
If you’re not thinking about the cloud security, you’re already behind. “Cloud infrastructure is ubiquitous today, and the security models are very different from on-premises systems.
That’s why these modules are part of cybersecurity training programs, organizations are moving to the cloud at a rapid pace, but they don’t fully understand the risks. There are different security models in AWS, Azure and Google Cloud and different ways people misconfigure security.
You’ll learn about cloud-specific threats in Modules Are Covered in Cybersecurity like misconfigured cloud storage buckets that expose sensitive data to the entire internet. It’s more common than you might think. You will learn about API security in cloud environment and proper secrets management.
Learn about Infrastructure as Code (IaC) and how to bake security into your infrastructure from day one, with the modules. You learn about security of containers and Kubernetes. Such technologies are becoming the standard way for companies to deploy applications.
Threat Intelligence and Analysis
Effective defense means understanding what threats actually exist. Threat intelligence modules help you to be aware of the threat landscape. You’ll gain practical skills to collect, analyze, and apply threat intelligence effectively.
In this chapter Modules Are Covered in Cybersecurity, you will learn about various threat intelligence sources including open source intelligence (OSINT), industry threat reports, dark web monitoring, and information sharing communities. You learn how to assess if threat intelligence is accurate and relevant.
The modules consist of threat modeling and attack trees. You don’t just become aware that threats exist, you learn how to think in a systematic way about how your specific organization could be attacked.”
You’ll learn about threat actors in Modules Are Covered in Cybersecurity who they are, what they care about, and what tactics they use. Nation states and financially motivated cyber criminals operate differently. Activists are not spies. You know who your likely enemies are so you can prioritize your defense by Modules Are Covered in Cybersecurity.
Security Operations Center (SOC) Management
Many online cybersecurity training programs cover individual security skills. Not so much teach you how security teams actually work together.
SOC modules include security monitoring, log analysis and security information and event management (SIEM) systems. in Modules Are Covered in Cybersecurity You learn to configure alerts that alert you about real problems, not false-positives that trigger alerts thousands of times a day and get ignored.
You will learn about the kill chain; the series of steps an attacker typically takes. It is better to detect and prevent early, rather than wait until they are inside your network and exfiltrating data.
Security teams use these Modules Are Covered in Cybersecurity for metrics and key performance indicators (KPIs). So how do you actually measure if your security program is working? It’s not so easy as it appears.
Why Online Delivery Matters for Advanced Training
You might ask yourself why advanced Modules Are Covered in Cybersecurity training is increasingly being done online. The truth is that when it comes to cybersecurity, online courses really do have some advantages that fit this field perfectly.
First, flexibility. Cybersecurity professionals often work odd hours. On-call duties are held by many. There’s real value in being able to study at 11 PM on a Tuesday while you’re waiting on an incident response to finish.
Second, you’ll have access to cutting-edge content. The security landscape changes fast. Online programs have an advantage over traditional classroom programs that are tied to academic schedules when it comes to updating curriculum.
Third, practical laboratory situations. The best cyber security online training is hands on labs where you are doing things and not just watching demonstrations. You configure firewalls, run exploits on vulnerable systems, analyze malware. These labs can be expensive to maintain, but are necessary to actually learn security Modules Are Covered in Cybersecurity.
Choosing the Right Program
There are a few things you want to look for when researching online courses for cybersecurity:
Is there a clear progression of topics from basic to advanced in the program? Do the instructors have real-world experience and are they real security professionals? Are they using the latest technologies and frameworks or are they still in 2015?
Are there hands-on labs in the program? If you are watching videos but not actually doing anything, you are not really learning. Can you view the content Modules Are Covered in Cybersecurity when it’s good for you or are there rigid class times? Are there any industry recognized certifications?
Ask them about their instructor team. “Taught by industry experts” means different things if the teacher is someone who read about security in a book vs. someone who has spent the last ten years running a SOC.
Taking the Next Step
Cyber security online training is a great way to build a career in Modules Are Covered in Cybersecurity if you are serious about it. People that the field needs and organizations are desperate to hire understand modern security practices. A sound training pays for itself in a short time.
Start from an honest assessment of where you are now. Are you a total beginner? Look for programs that begin with the basics. Already in IT and want to break into security? Look for programs that are designed for that transition. Already a security professional looking to advance? Check for advanced certifications & specialized training.
The modules are covered in cybersecurity training with progression in mind. Don’t try to leap ahead. Basic skills are very important. If you skip cryptography and go straight to advanced threat defense, you’re going to struggle because you’re missing critical context.
Your cybersecurity education should be continuous. The field is always evolving. The best security professionals are those that never stop learning. That’s what online courses for cybersecurity are for. You can get higher education while you work full time.” You can refresh your skills as the threat landscape evolves. You can focus on what you find most interesting.
Final Thoughts
The promise of Cyber security online training isn’t that you’ll be invulnerable to attack, or that you’ll single-handedly stop every threat. The promise is simple: you’ll understand modern Modules Are Covered in Cybersecurity well enough to make informed decisions, apply effective controls, and help your organization manage its risk.
Cyber security training takes a systematic approach to the modules, building up knowledge layer by layer. Each module is connected to others. All ideas support each other. By the end of solid advanced training you know not only about network security, cloud security and incident response. You know how all these Modules Are Covered in Cybersecurity things come together in a holistic security strategy.”
Whether you’re new to cybersecurity or want to take your existing skills to the next level, the best online courses for cybersecurity can change your career. The question isn’t, “Should I invest in training? The question is Modules Are Covered in Cybersecurity: which training program gives you the practical skills that you need in the real world.