Introduction
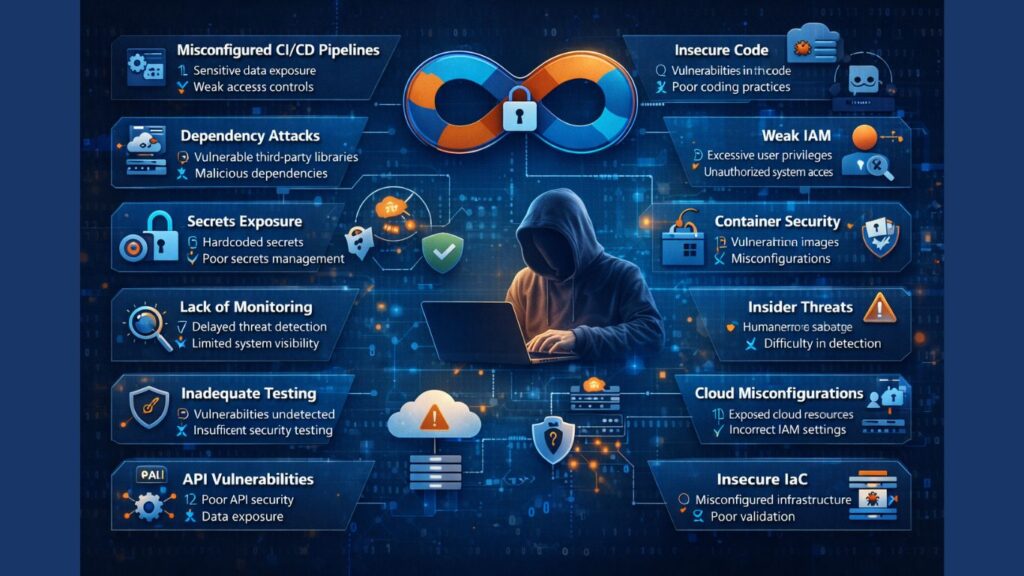
DevSecOps is now an important way to build secure applications by including security in every step of the development lifecycle. This is because software development moves so quickly these days. H2k Infosys stresses how important it is to align development, security, and operations to lower risks and raise the quality of software as a whole. As more and more businesses use this model, it’s important to know about cybersecurity risks in DevSecOps in order to keep strong protection against new cyber threats.
DevSecOps adds security to continuous integration and continuous delivery (CI/CD) pipelines, but this quick and automated method can make things less safe. Without the right controls, even small mistakes in configuration can lead to big problems. This Cyber security training courses blog talks about the biggest cybersecurity threats in DevSecOps environments and how businesses can best protect themselves from them.
Understanding DevSecOps and Its Security Challenges
DevSecOps builds on DevOps by adding security practices to every step of the development process. Instead of being the last step, security becomes a shared duty among teams.
But this method adds a number of cybersecurity risks to DevSecOps, such as:
- Cycles of quick deployment
- A lot of dependence on automation
- Cloud-native systems that are hard to understand
- Tools and teams that are spread out
If these things aren’t handled properly, they make security gaps more likely.
1. Misconfigured CI/CD Pipelines
Misconfigured pipelines are among the moThe most common cybersecurity threats in DevSecOps settings. These pipelines make the processes of building, testing, and deploying automatic.
Why It’s Dangerous:
- Exposing private credentials
- Getting into deployment tools without permission
- Higher chance of code being changed
Mitigation:
- Use role-based access control
- Use vaults to keep your credentials safe.
- Do audits on a regular basis
2. Insecure Code and Vulnerabilities
Bad coding habits are a big reason why DevSecOps is so risky for cybersecurity. When developers are under a lot of pressure, they might not pay attention to security.
Why It’s Dangerous:
- Introducing weaknesses that can be used
- Quickly putting out code that isn’t safe
Mitigation:
- Use tools that scan code automatically
- Follow the rules for safe coding.
- Do peer reviews
Online classes in cyber security help developers improve their skills in writing secure code.
3. Dependency and Supply Chain Attacks
Third-party libraries are used by many modern apps, which makes DevSecOps more vulnerable to cyberattacks.
Why It’s Dangerous:
- Dependencies that are weak or harmful
- Not being able to see external parts
Mitigation:
- Use tools that scan for dependencies
- Make sure libraries are always up to date.
- Check that external code sources are valid
4. Weak Identity and Access Management
One of the biggest cybersecurity threats in DevSecOps settings is not having the right access controls in place.
Why It’s Dangerous:
- Access to the system without permission
- Too many permissions for users
To lessen:
- Enforce access with the least amount of privilege
- Use more than one way to log in
- Keep an eye on how users act
5. Secrets Exposure
Secrets management failures significantly increase cybersecurity risks in DevSecOps.
Why It’s Risky:
- Hardcoded passwords in code
- Exposure of API keys
Mitigation:
- Use secure vaults
- Rotate credentials regularly
- Avoid storing secrets in plain text
6. Container Security Issues
Containers are widely used, but they also introduce cybersecurity risks in DevSecOps.
Why It’s Risky:
- Vulnerable container images
- Misconfigured container environments
Mitigation:
- Scan images regularly
- Use trusted base images
- Apply runtime security controls
7. Lack of Continuous Monitoring
Without proper monitoring, cybersecurity risks in DevSecOps can go unnoticed.
Why It’s Risky:
- Delayed threat detection
- Lack of system visibility
Mitigation:
- Implement real-time monitoring tools
- Use logging and alerting systems
- Conduct regular audits
8. Insider Threats
Human factors contribute heavily to cybersecurity risks in DevSecOps.
Why It’s Risky:
- Misuse of access privileges
- Accidental data leaks
Mitigation:
- Monitor user activity
- Limit access permissions
- Train employees on security awareness
9. Inadequate Security Testing
Skipping testing increases cybersecurity risks in DevSecOps environments.
Why It’s Risky:
- Undetected vulnerabilities
- Weak application security
Mitigation:
- Integrate testing into CI/CD
- Use automated security tools
- Perform penetration testing
10. Cloud Misconfigurations
Cloud environments are a major source of cybersecurity risks in DevSecOps.
Why It’s Risky:
- Publicly exposed resources
- Weak access policies
Mitigation:
- Use cloud security tools
- Regularly review configurations
- Follow best practices
11. Lack of Security Awareness
A lack of knowledge increases cybersecurity risks in DevSecOps across teams.
Why It’s Risky:
- Human errors
- Poor decision-making
Mitigation:
- Conduct training programs
- Encourage security-first mindset
- Promote awareness
A cyber security course with placement can help professionals gain practical expertise.
12. API Security Vulnerabilities
APIs are critical but often overlooked, leading to cybersecurity risks in DevSecOps.
Why It’s Risky:
- Weak authentication
- Data exposure
Mitigation:
- Secure API endpoints
- Use encryption
- Monitor API traffic
13. Automation Risks
Automation can amplify cybersecurity risks in DevSecOps if not properly managed.
Why It’s Risky:
- Rapid spread of vulnerabilities
- Errors in automated scripts
Mitigation:
- Validate automation processes
- Add security checks
- Monitor workflows
14. Compliance Failures
Regulatory non-compliance is another source of cybersecurity risks in DevSecOps.
Why It’s Risky:
- Legal penalties
- Data protection failures
Mitigation:
- Follow compliance standards
- Conduct audits
- Maintain documentation
15. Insecure Infrastructure as Code (IaC)
IaC misconfigurations introduce serious cybersecurity risks in DevSecOps.
Why It’s Risky:
- Incorrect infrastructure setup
- Lack of validation
Mitigation:
- Scan IaC templates
- Use version control
- Implement approval workflows
Best Practices to Reduce DevSecOps Risks
To minimize cybersecurity risks in DevSecOps, organizations should adopt proactive strategies:
- Shift security left
- Automate security testing
- Implement zero trust architecture
- Continuously monitor systems
- Invest in training through online classes cyber security
Importance of Training
Training helps reduce cybersecurity risks in DevSecOps by improving skills and awareness.
Benefits include:
- Better risk management
- Stronger security practices
- Reduced human error
A cyber security course with placement ensures hands-on learning and career readiness.
Future of DevSecOps Security
The future will bring advanced solutions to tackle cybersecurity risks in DevSecOps, such as:
- AI-driven threat detection
- Automated compliance tools
- Enhanced cloud security systems
Organizations must stay proactive to handle evolving threats.
Conclusion
DevSecOps has transformed software development, but it also introduces multiple cybersecurity risks in DevSecOps environments. From pipeline misconfigurations to cloud vulnerabilities, each risk demands careful attention and proactive management.
By implementing best practices, improving awareness, and investing in training like online classes cyber security and a Cyber security course with placement, organizations can significantly reduce risks and build secure systems. Staying ahead of cybersecurity risks in DevSecOps is not just an option, it is a necessity in today’s digital landscape.